(see also “Enterprise patterns: AGA” http://improving-bpm-systems.blogspot.ch/2014/03/enterprise-patterns-aga.html)
Part of enterprise architecture is about establishing practices (processes and decisions) to govern (or to steer) some domains of enterprise activities. This blogpost provides a generic approach to setup domain governance.
1 Generic approach
Domain governance covers the entire life-cycle of the domain primary-artefacts.
Decompose the whole life-cycle into phases (or stages).
Each phase comprises several primary-artefacts, rules, activities and processes.
Responsibilities to own these primary-artefacts, rules and processes must be assigned to somebody.
Responsibilities to perform these processes and activities must be assigned to somebody.
All these responsibilities are grouped into several roles (under some considerations including “separation of duties”).
Domain stakeholders are assigned to these roles.
Various documents to support primary-artefacts are identified and their life-cycles are considered as well (roles to write, use and approve these documents).
Domain governance makes explicit primary-artefacts, supporting-documents, roles, rules, processes, phases and life-cycles.
Domain governance specifies dependencies with other domains governance practices established in the enterprise.
2 EXAMPLE TW
2.1 Context for Technology Watch function
A typical IT Department uses hundreds digital technologies, tools, products and services from third-party companies to provide highly efficient digital business solutions. There are complex dynamic dependencies between those technologies, tools, products, services, companies and digital business solutions. For example, companies may merge or go bankrupt, products may be discontinued, tools may be exposed to security bridges, new technology may make an existing technology obsolete, etc. All of these may have a negative impact on some digital business solutions or, on the contrary, create an opportunity for improving some digital business solutions.2.2 Technology Watch (TW) vision and mission
TW vision – timely provisioning IT industry information for decisions related to strategic, tactical and operational aspects of digital business solutions.TW mission – systematic capturing, analysing, disseminating and exploiting information about used digital technologies, tools, products and services.
2.3 TW governance
TW function operates with three primary-artefacts:
- Critical Watch Artefact (CWA) – a technology, tool, product, service, company to be watched
- TW-Event (TWE) – a fact of detecting something interesting about a particular CWA
- TW-Decision (TWD) – a decision taken for a particular TWT
The relationships between these primary-artefacts is depicted in figure BELOW. Monitoring of a CWA may detect hat something of interest has happened with this CWA and thus to trigger the initial analysis. The latter may lead to a deeper investigation and a decision for dispatching some ITSM processes.
Figure 1
3 EXAMPLE SOA Governance
3.1 SOA Governance vision and mission
SOA vision – considerably speed-up the delivery and evolution of software-intensive digital business solutions.SOA mission – industrialise the delivery of software-intensive business solutions as a set of autonomous components (i.e. services).
3.2 SOA Governance approach
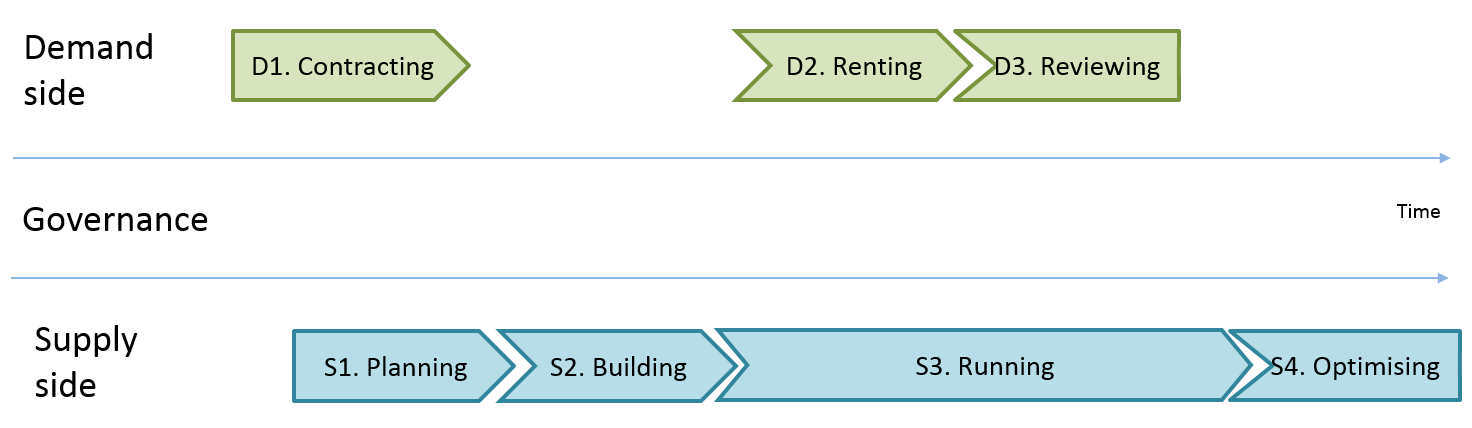
SOA governance is balancing the demand side and supply side. Some service providers (supply side) may be temporary not consumed. Some service consumers (demand side) may use the same service provider. A service consumer (demand side) may use a few service providers at the same time.
Figure 2 Links between service consumers and service provides
The life-cycle of service demand comprises the following phases: D1. Contracting, D2. Renting and D3. Reviewing.
The life-cycle of service supply comprises the following phases: S1. Planning, S2. Building, S3. Running and S4. Optimising.
3.3 Scenarios for service provisioning
There are three scenarios in the service provisioning.1. Scenario “sur mesures” or “make-engineer-to-order” - design a new service and deploy; coordination between phases in this scenario is shown in figure below.
Figure 3 Scenario “sur mesures” for service provisioning
2. Scenario “adaptation” or “make-build-to-order“ - tailor an existing service and deploy; coordination between phases in this scenario is shown in figure below.
Figure 4 Scenario “adaptation” for service provisioning
3. Scenario “prêt-à-porter” or “make-build-to-catalogue” - build some services before actual demands; coordination between phases in this scenario is shown in figure below.
Figure 5 Scenario “prêt-à-porter” for service provisioning
3.4 Stakeholders and their participation into the service demand and service supply life-cycles
Demand side roles are:- demand initiator, e.g. a Head of Department
- service consumer, e.g. staff member from a Department
- service owner, e.g. somebody from the IT department
- service implementer, e.g. a preferable partner
- service operator, e.g. a preferable partner or the IT Department (actually, its OPS group)
- service auditor, e.g. somebody from the IT department, EA function or third-party
Figure 6 Participation of some roles
The detailed participation of various stakeholders is shown below in accordance with the RACI technique.
service
demand
|
service
supply
|
||||||
contracting
|
renting
|
reviewing
|
planning
|
building
|
running
|
optimising
|
|
Demand initiator
(demand side)
|
RA
|
RA
|
R
|
C
|
I
|
I
|
C
|
Service owner
(supply side)
|
C
|
C
|
C
|
RA
|
C
|
I
|
R
|
Service implementer
(supply side)
|
C
|
-
|
-
|
-
|
RA
|
C
|
C
|
Service operator
(supply side)
|
C
|
C
|
I
|
-
|
C
|
RA
|
C
|
Service consumer
(demand side)
|
C
|
I
|
C
|
-
|
C
|
I
|
C
|
Service auditor
(governance side)
|
I
|
I
|
A
|
I
|
-
|
I
|
A
|
3.5 Outline of the process
The coordination between the two life-cycles is shown in figure below. The pink numbered markers show the sequence in the control flow (only the “happy” path). The solid arrows are used within each of the life-cycles. The dashed arrows are used between the two life-cycles.
Figure 7 Coordination between two life-cycles
This figure is the base for defining the domain documents and their life-cycles as well (thus governing bodies which approve these documents).
Thanks,
AS









No comments:
Post a Comment